Open Security Summit – Secure by Scenario
April 14 2021
Scenario:
Privacy audit company is visited by a person following a data breach. This person would like a 3 quotes for strategies, based on actions that can be done within 24 hours, 48 hours and 7 days. One team worked on strategies after a data breach and the other team worked on strategies following a SIM-swapping attack.
Post breach strategies:
24 hours: Recon, establish threat model. Phishing awareness & recommend changing passwords.
48 hours: Implement credit monitoring, potentially apply for a credit freeze. Inform banks / credit services of potential fraud around this client. Query breached company for additional details as to what was released. Run automated scans for additional recon & threat assessment.
7 days: Implement strategies going forward, such as canary tokens. Configure & train on the use of password manager & 2FA. Introduce to legal counsel & privacy cleanup services. Provide client with training on subject data requests.
Post SIM-Swapping strategies:
24 hours: Stop attack / block access to rogue SIM. Lock all accounts using SMS 2FA.
48 hours: Investigate how attack propagated & telecom provider. Full forensics on the device & on affected accounts. Change passwords on affected accounts.
7 days: Training for online behaviour & security awareness. Add further layers of security to the SIM card & replace SMS as 2FA method. Provide help with legal recourse.
March 10 2021
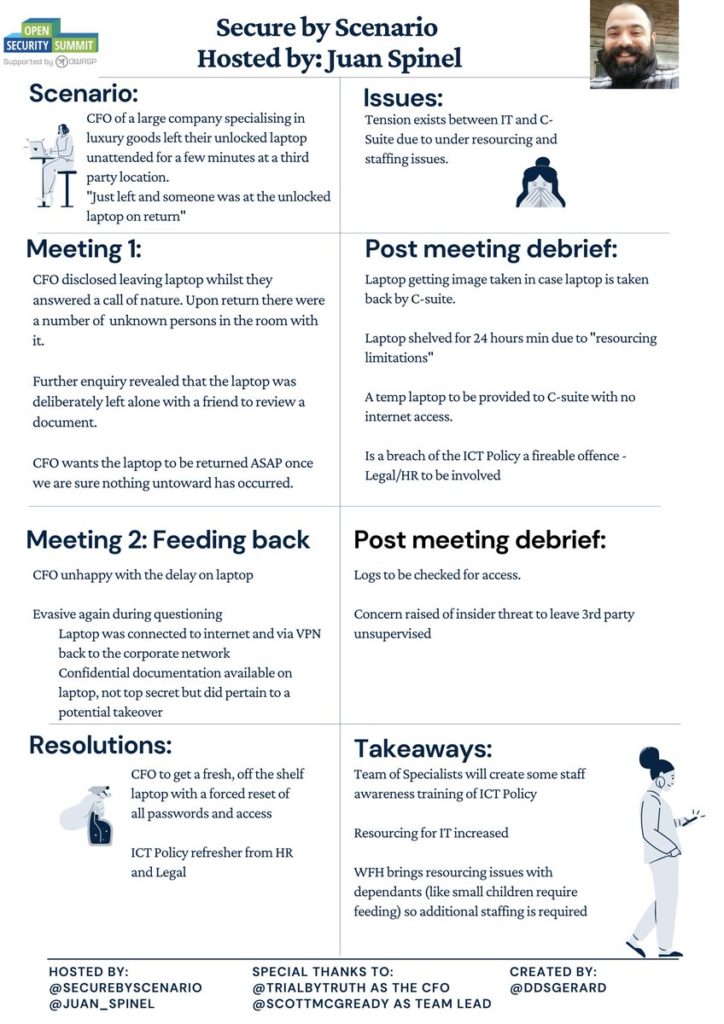
Scenario: CFO left corp laptop unattended, suspects other people may have accessed it. IT is understaffed and unable to run forensics immediately. Through cooperation & negotiation, both parties agree on forensic measures and CFO is able to work again.
GrimmCon 0x3 – Dec 30 2020
GDPR – Strategies in Failure
BeerCon 2 – Oct 29 2020
GDPR – The Good Intentions, Bad Implementations & Ugly Loopholes