Why KeePassXC?
Most of my experience with password managers lies with KeePass. For an enterprise environment it is simple to use, easy to deploy and fairly lightweight. For my personal use I can take advantage of its portability and not worry about phishing too much, as I tend to type out websites directly when something sketchy comes around. For work, VMs and other users however, I recommend KeePassXC now. It offers some advantages to KeePass, namely an easier interface, browser integration and TOTP.
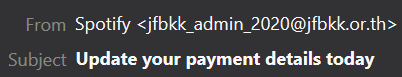
The browser integration provides phishing protection => if users click on links asking for credentials, the extension will not recognise the domain and therefore not provide credentials. Along with the easier interface, this means users are more likely to avoid password reuse and less likely to fall for phishing attempts.
First Steps
The KeePassXC team have a great introduction to their password manager, covering details from setting up a database to the configuration of the browser integration. I highly recommend taking a look there before doing the install, even if just to make yourself aware of the different interface. You can find their getting started guide here.
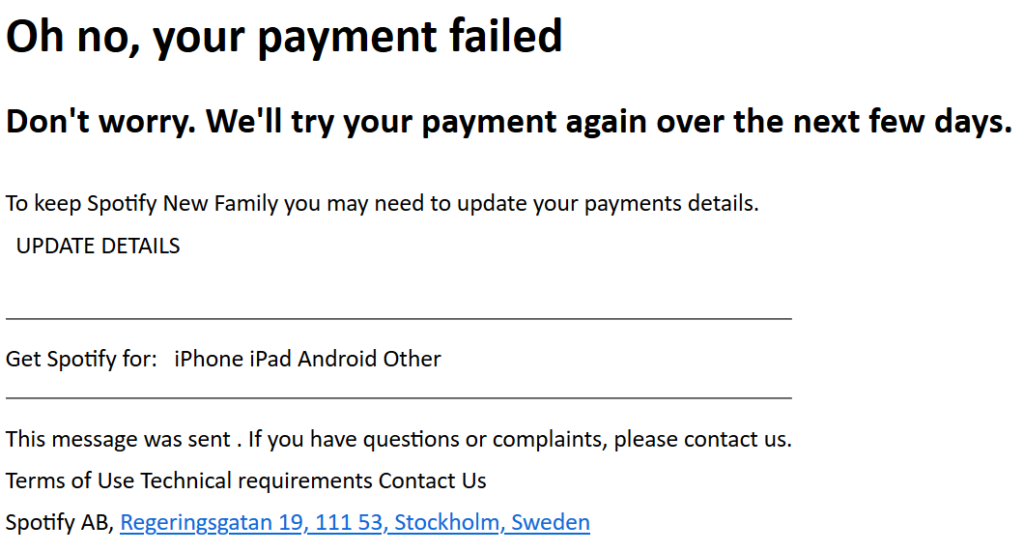
Now, following the steps from the KeePass guide there are some differences in the procedures. The first is the key transformation, instead of telling the system how many iterations you want, KeePassXC suggests choosing how long it takes to decrypt the database.
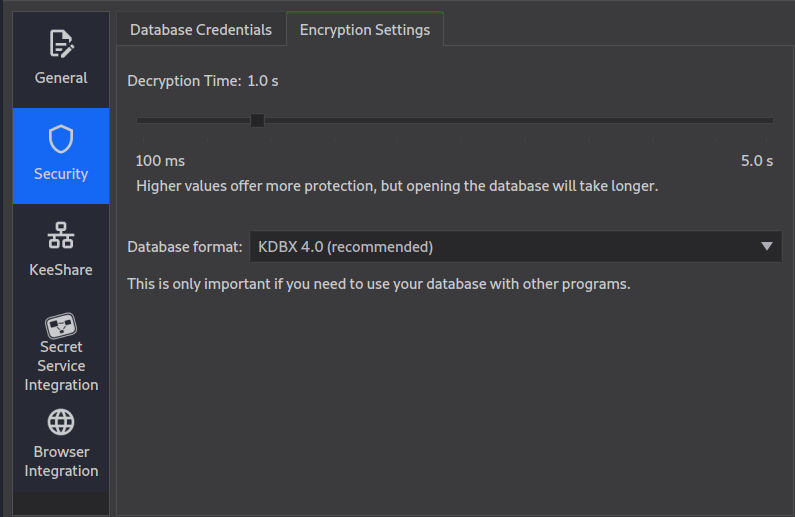
Unlike KeePass, KeePassXC doesn’t provide password templates. nor does it offer the ability to generate a password from the previous password (useful for services with character or length limitations). The password generator takes the last used settings. My recommendation is to check the box to avoid lookalike characters (for those times you need to type it out).
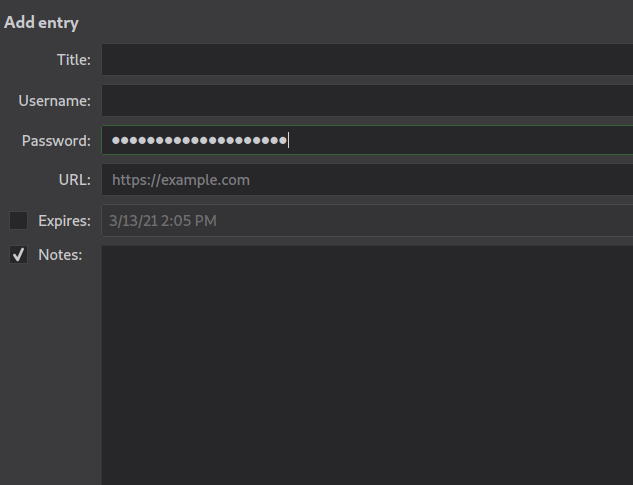
Same as with KeePass, KeePassXC allows entries to autoexpire. This is not checked by default, in my use of the application, it does not stay checked when making several entries. The preset expiry times include 1, 2, 3 weeks, months and years.
Same as with KeePass, I recommend renewing your passwords at 6 month intervals, but at least once a year.
TOTP
Unlike KeePass, KeePassXC comes with TOTP support out of the box. While arguably this is not great as it means you are getting all your authentication tokens through the same medium, it does protect your accounts from brute forcing attacks. You can’t set TOTP from the entry window, but after creating the entry right click => TOTP =>Setup TOTP. When generating your tokens, tell the web service you can’t scan the QR code, and enter the secret into the TOTP window.
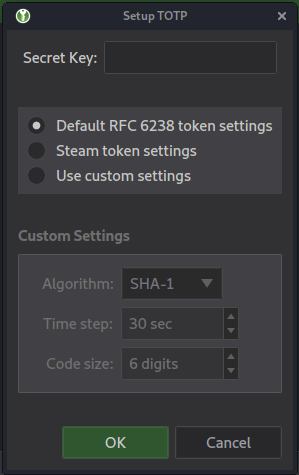
It is worth mentionning that you can get the secret from KeePassXC. Not the most secure solution but I can see this being useful for teams connecting to client environments, as the database can be shared through KeeShare with those people who need access to it. With the browser extension, this means seamless logging in to services as all the credentials come from a single place, (and the database can be locked with a passphrase & hardware token).
KeeShare
KeeShare sort of takes the need for cloud sync away accross devices, however my limited experience with this feature was not great. Most likely due to user error and limited time / infrastructure to play with it, it is worth knowing that the KeePassXC team have documented it quite well over here.
Nice to know
You can save credentials from the browser extension directly to your database. These will be in a default “browser credentials” group. You can order them into whatever folder you want if you actively use the standard interface to find them faster.
By default, autotype is enabled in KeePassXC, but with no assigned shortcut. With the browser extension I have not found any reason to activate it. Specially after the shenanigans with KeePass spouting my credentials into a couple services.
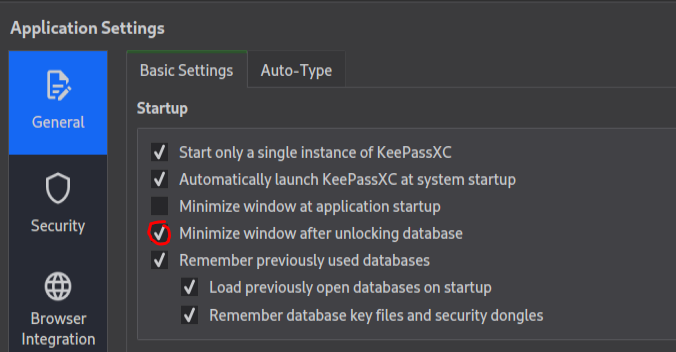
The browser extension requires the database to be unlocked in order to use the credentials. The icon turns green when the connection between the extension and the data base is active, and grey if the connection is not present. I have found it particularly useful to be able to hide the window once it has been unlocked as it lets me keep an uncluttered desktop, and the browser lets me know if anything is the matter.
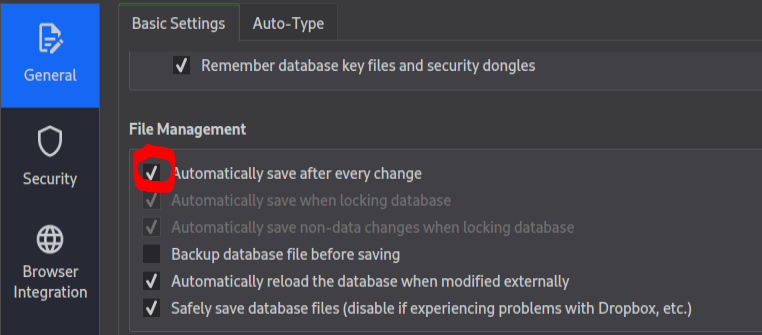
By default, the database will be saved after every change (new entry, password change, etc.). I’ve found this behaviour useful, but worth knowing if you have a long decryption time it can slow down your machine. The behaviour can be medified in the Application Settings => File Management.
Sadly, unlike KeePass, there is no option to show expired / expiring soon entries upon loading up the interface. The entries will have a different icon showing that the entry has expired and the title will be crossed through.

KeePass or KeePassXC?
I think it really comes down to the user. Both offer similar levels of protection for the users’ databases, they differ mainly in what they offer out of the box. Neither solution has been ported to Android or iOS which means regardless of what you pick, there will always be another party accessing your passwords. I believe KeePass will continue to have its place in enterprise environments where it outperforms the XC variant through a slimmer interface. KeePassXC does provide a nicer experience for first time users, with default settings that make it easy to use from the get-go. As long as you don’t use TOTP, you can use both with the same database and decide later on.